By Alfredo Oliveira and David Fiser
Key Takeaways
- We found 492 MCP servers with no client authentication or traffic encryption.
- Successful attacks against these servers lead to data breaches, leaking sensitive information such as company proprietary information and customer details.
- Organizations that use MCP servers must not expose them on the network without an additional security layer (authentication/proxy).
- Recommendations for mitigating the risks include exposure management, with limited permissions for the MCP server.
Organizations should be proactive in their defense and watch for every possible crack in security. Our latest research looks specifically at security issues that may occur when deploying Model Context Protocol (MCP) servers. Companies should keep their eyes open for the security risks that arise when exposure management is not properly implemented.
The MCP architecture introduces a significant security issue when servers are exposed to the network without authentication. By default, the client is not required to use authentication to access the MCP server, as shown in the connection flow below:
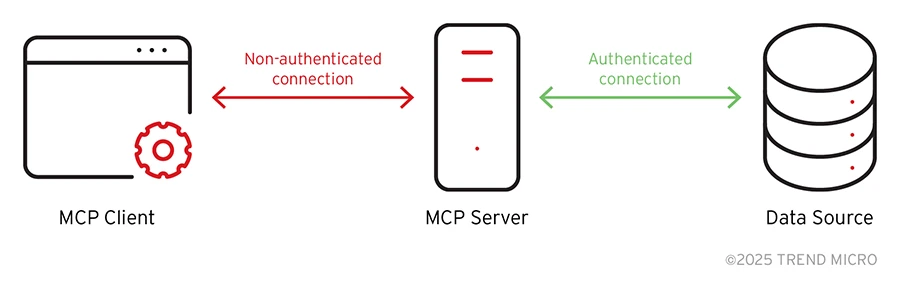
Figure 1. MCP connection flow
No open…